To make it short, in clear-text. if you’re interested how, continue ![]()
The early bird
Back in the 1990s, I was working at a really huge ISP. We dealt with DDoS and the usual attacks, along with a lot of abuse. On one occasion, a user was blackmailing the company daily.
Our Director came down to us ! and asked if I could take a look into the situation. I was lucky! I found out the email used to send the blackmail was hosted somewhere else in the world, and none of my friends had connections to the hoster.
Suddenly, I had an idea based on the used username.
People generally use the same email/username everywhere ![]() . So, I manually logged into this other account and tried to recover his user login on the other server. Yes, a few moments later, I had a recovery link in his mailbox (on our servers). I changed his local mail account and changed the password for the other access.
. So, I manually logged into this other account and tried to recover his user login on the other server. Yes, a few moments later, I had a recovery link in his mailbox (on our servers). I changed his local mail account and changed the password for the other access.
It didn’t take 30 minutes before my Director came again and asked how I did that. “This is magic!” he said. The guy had called, apologized profusely for the problem he caused, and asked to recover his password. You didn’t need to call the police, nor were they interested in such things. I didn’t give away any private information on the other account; I just changed the passwords. Today, this properly would be a crime and you’re punished, but in 1995, no one cared.
My friends ask me why I am so paranoid about privacy. With 30+ years of experience, it’s not because I’m selling drugs or doing bad things, but I have a lot of stories to share (which I can’t really) due to confidential cases. I’ve learned how to set up and maintain a mail server, and I’ve also learned about the dark side.
Today, my things are post-quantum encrypted. Not that I have something to hide, but just because I can do it. Furthermore, I also find it questionable when certain groups exploit my know-how for other purposes. On the other hand, I also find it questionable how the state monitors us and assumes we are all criminals. But that is another topic.Back to Email
RFC
RFC 822 specification defines an electronic message format consisting of header fields and an optional message body. The header fields contain information about the message, such as the sender, the recipient, and the subject. If a message body is included, it is separated from the header fields by an empty line (\r\n).
The following example illustrates a message in the RFC 822 message format: [Example]
From: someone@example.com
To: someone_else@example.com
Subject: An RFC 822 formatted message
This is the plain text body of the message. Note the blank line
between the header information and the body of the message.
How we send emails manually:
1.) telnet mail.mymailserver.com 25
Use the HELO command to tell the mail server which domain you are coming from:
HELO gnoppix.org
2.) Now we need to state from which address this email will be sent.
RCPT TO: someone@example.com
3.) we can start writing some subject and body. To do that we need to use the DATA command. First type DATA followed by Subject: and the body. Once done, enter . to send the email to be queued.
DATA
Subject: Sending an email using telnet
Hello,
Here is my body? Do you like it?
cheers
.
4.) Do not forget “.” at the end of the message. To quit, type:
quit
Now you can check your mailbox to ensure that it has sent correctly.
How it looks like
You log into the Mailserver as Admin, you look for something like this:
root@mail:/var/mail/your-data-dir/data/domains/gnoppix.intern/username# ls -l
total 8
drwxr-xr-x 9 mail mail 4096 Nov 7 00:36 Maildir
drwxr-xr-x 2 mail mail 4096 Jul 26 09:51 sieve
We move into Maildir:
total 372
drwxr-xr-x 9 mail 4096 Nov 7 00:36 .
drwxr-xr-x 4 mail 4096 Jul 30 04:50 ..
drwxr-xr-x 5 mail 4096 Jul 26 11:15 .Drafts
drwxr-xr-x 5 mail 4096 Oct 6 06:28 .Junk
drwxr-xr-x 5 mail 4096 Jul 26 11:15 .Sent
drwxr-xr-x 5 mail 4096 Jul 31 06:29 .Trash
drwxr-xr-x 2 mail 4096 Nov 21 02:38 cur
-rw-r--r-- 1 mail 10796 Nov 7 00:36 dovecot-uidlist
-rw-r--r-- 1 mail 8 Jul 26 09:51 dovecot-uidvalidity
-r--r--r-- 1 mail 0 Jul 26 09:51 dovecot-uidvalidity.6884a540
-rw-r--r-- 1 mail 2584 Sep 26 22:40 dovecot.index
-rw-r--r-- 1 mail 282700 Nov 7 00:36 dovecot.index.cache
-rw-r--r-- 1 mail 7780 Nov 7 00:36 dovecot.index.log
-rw-r--r-- 1 mail 2208 Sep 27 06:28 dovecot.list.index.log
-rw-r--r-- 1 mail 1479 Nov 7 00:36 maildirsize
drwxr-xr-x 2 mail 20480 Nov 7 00:36 new
-rw-r--r-- 1 mail 23 Jul 26 09:51 subscriptions
drwxr-xr-x 2 mail 4096 Nov 7 00:36 tmp
The interesting part is the new folder, this is where all new mails going in, the cur folder is if a user got the new email and read it.
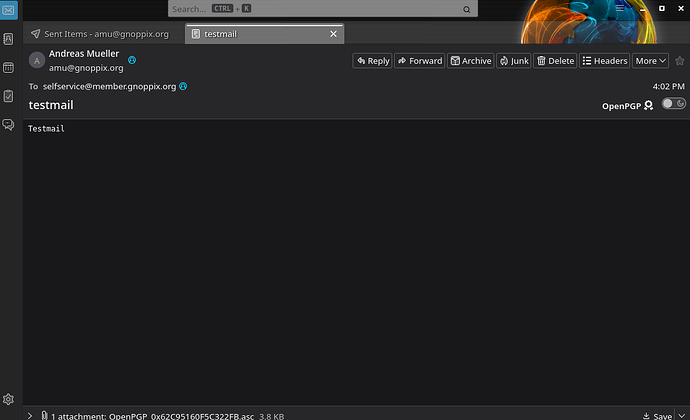
Sending a testmail
Check on the other DST server, the email reached the box we can check the logfiles.
2025-12-09T21:02:35.988Z [12E5E763-137B-4544-AB40-AE83D8ACADE9.1] 7.112.28.96:53648%gnoppix.intern () <amu@gnoppix.org> -> <selfservice@member.gnoppix.org> - [-1.89][<35ebca53-1afe-4633-980b-959dbdc69de0@gnoppix.org>] 250 Message Queued (12E5E763-137B-4544-AB40-AE83D8ACADE9.1) (12E5E763-137B-4544-AB40-AE83D8ACADE9.1)
Yes, that looks cryptic, but the importance here is the 250 Message Queued status.
Unfortunately, we do not know now if the message is flagged as spam or contains a virus and has been moved into quarantine.
Therefore, we can check if the email arrived in the recipient’s inbox (or the new mail folder).
ls -l
-rw-r--r-- 1 mail mail 12640 Dec 9 21:02 '1765314156.M5581P1874745.9925427d1982,S=12640,W=12853'
that may work (it’s a read/only email only account, for this I removed the delete all incoming emails function)
We can read the hole email now in plaintext with :
more 1765314156.M5581P1874745.9925427d1982,S=12640,W=12853
And here is the content, we’re looking for:
Date: Tue, 9 Dec 2025 16:17:50 -0500
MIME-Version: 1.0
User-Agent: Betterbird (Linux)
Content-Language: en-US
To: selfservice@member.gnoppix.org
From: Andreas Mueller <amu@gnoppix.org>
Subject: testmail
Content-Type: text/plain; charset=UTF-8; format=flowed
Content-Transfer-Encoding: 7bit
X-Haraka-Karma: score: 1, connections: 1, history: 0, asn_score: 1, asn_connections: 2, asn_good: 1, awards: 131, fail:rcpt_to
X-p0f-Result: os="Linux 2.2.x-3.x" link_type="Ethernet or modem" distance=9 total_conn=5
X-Rspamd-Bar: /
X-Rspamd-Report: DMARC_POLICY_ALLOW(-0.5) XM_UA_NO_VERSION(0.01) R_DKIM_ALLOW(-0.2) MIME_GOOD(-0.1) R_SPF_ALLOW(-0.2)
X-Rspamd-Score: -0.99
X-Haraka-GeoIP: JP
X-Haraka-GeoIP-Received: x.x.x.x (censored)
Testmail
What also works, since I’m root/admin I can run
mutt -f Maildir
and get:
i:Exit -:PrevPg :NextPg v:View Attachm. d:Del r:Reply j:Next ?:Help
Date: Tue, 9 Dec 2025 16:17:50 -0500
From: Andreas Mueller amu@gnoppix.org
To: selfservice@member.gnoppix.org
Subject: testmail
User-Agent: Betterbird (Linux)Testmail
I worked in my early years at ISPs, managing mail servers.
Authorities would come in (with a court order) and request the content of User X’s mailbox. As an admin, you would compress the folder and put the zip file onto a USB drive. This took less than a minute.
Also, surveillance was often requested, especially since the SMTP protocol became encrypted. A common method was simply to add a so-called alias (a copy of all incoming/outgoing mail):
alias: user-x@domain.com, surveillance-target@isp-admin.com
In this case every incoming email to user-x went automatically to surveillance-target@isp-admin.com without the user-x knowing emails are copied.
Solution ?
Today, I built a secure email server for a project that handles all the features modern mail servers require: checking for viruses, spam, RBL testing, AND encrypting content. Call me a freak but AI is included too, OSS AI of course.
Instead of using the almost 40-year-old solution of saving emails in cleartext, the emails are now stored in a database, completely encrypted.
I’ve sent an email to myself take a look:
Message-ID: 9e211740-5062-489d-9b80-54be68a87d32@gnoppix.org
Date: Tue, 9 Dec 2025 17:16:12 -0500
MIME-Version: 1.0
User-Agent: Betterbird (Linux)
Content-Language: en-US
To: amu@gnoppix.org
From: Andreas Mueller amu@gnoppix.org
This is an OpenPGP/MIME encrypted message (RFC 4880 and 3156)
--------------WpiPkbXG9D7U6Inn2A8qy0e2
Content-Type: application/pgp-encrypted
Content-Description: PGP/MIME version identification
Version: 1
--------------WpiPkbXG9D7U6Inn2A8qy0e2
Content-Type: application/octet-stream; name=“encrypted.asc”
Content-Description: OpenPGP encrypted message
Content-Disposition: inline; filename=“encrypted.asc”
-----BEGIN PGP MESSAGE-----
wcFMA4C/RLfgTwSqAQ//aEN+jAH3fpX7yZGnmRU2mXY30UNZVfKCdI7XVKWSnqZHPe9RhkvyLtNH
/RCNga3mB6Zn3A6gMr7UgvcTZGn6uNALwljkKXBsRs114Q5OChEnqZUSn+6gI5y2YgBC+GicfPu3
LVZuMifWoq5rSTo27s/bX+P30DTufqgNCaRg9uD64leKWs0GlI7PkhT+XGokmeNmWFhUagmw3SIq
CTiYoIGa/nl9zSKrl5AvEY6xdg2XT1u8tJlpN7rx6zCU0RmvTZYn4+uzj98ds34Z2LxIW4TYT2KN
OSys9zuq1sT1e11RIyWzTLL4F3dDn7QbvW8tint+91tLqHobTVLffx+ImaY5E6e5p5GjoYqF9NVi
erNquLGgAS3zpkwAHNDOyfW9jHR96Mi99QDruLJ91Ds3hDgE6MH34/Ak13C68QRItzkIDnSmsQhF
qSUf5JDXICusDfXQE/8sQ8FCClPSrH25+b8UjNwASBoiwgdU05QXDqe4LU/Zr8kTB8SavBzFgdrj
cwkEmeMy3xPB0fMdP0ri+pzMVH8NSLugR5b/W7rtFJYIEbppKJwj4Xhs1F4qW3y/H3SMfDs3UPhm
JwDtg9BBr9slRGCTQq/EYyTZnyZrVhEsI6/Bt+vyq8fyh2rqYc/teRdhIa9YR6rMEpFpX+zxN8He
oqQ1/Yl+Met+R2/b/3rBwUwDgL9Et+BPBKoBD/9A0k7Tr7yKcNGf27M9XxahM+DAEWs7jVdNNcVr
FW+zNZTXe25caNgO6w5qQK8cIjLjzw9wZNn8JUJDd1TOIDbgePyVZmeBOUpQa8wx12+EKNuVNLkT
B/meIk9GeCic+kD9KxJdWV6gQ+k82unxmMDba/g90+LK0QmVBgrMYXISa4lCP6e8Lg0i+WIS0VsJ
V1dOdDfX2wWW6RPKElj/+UhCY+rSsIRTFyIrJWJ3cxTSV3UUTEQr6cG/0UPLjdVURHMZ5bFIvDpz
bkyNJ2GnXxk5ksEJmNfQPrM5PBouffUfTIC6s3lGPUsIfcHuJ3IqojX4sjAVzf81JCrwlHDcUQ2D
6mfXGzC988rAIezaeBgM8x4FP/lYU4hvZ1Ie27fjxtVCrVZ3b46mrS+zUrXdka3XxPcDmlhxvQVX
NwSDNZnomFal7xjA5SKWX/6XPH9IMmjoYkjERAFbxZr89ioQcrQNdk/zkJAIFgqRdWlRlvr5I+4w
LhOBbw1pJiwuYvY/Wze8/S/D6uTA+2VraODQnofvBs8OKm9sA9j9sbJPjH8A0E3e1J+OaW5sAU5h
Ovgopkay8smjRgW6xo87WMXVovuNansFvgTnKBIazpLLUHiRVXqtZe8Q/dt8DiMr/88U+5tzIHXp
IHYTcWSJhizfpvGI/CFz5h1L5HyH6xjNgqpXq9LUxQE0wNBWYfp8yeYUgbuJcC2ZS1s+MsIsJ/Wq
24HdfnA+2Lwt9xBj7YId3LEvIr6fY5uk5rImXMGS90ualb9lm3ZxAQIHSeXPG3XBcyZI6oRIWFeB
jIDxjNDyPJoPB+mJsDqRJpedDeEv/KgXeGIlIxyscfQr8F1cEQovYZ+BHzIGpcxHQGhSflVKUjRU
X54qD7Yl6uyICxAiYADNEfEpU+SWQ8DeOsMPAmIe9HoVHgw1rwkK2kikN15Tok/GJFZigRyXaekd
KIJVIPQho5oHidWCHYiVwCHjbiRH8cXyvDVcZ10WDhj4on8cyQj9kQuMGBAPJTFlaAzFmbgJ0SVU
fcL2fhqrs6FynulJwBooyxCUaVtcjHxMuKwyVj5fuHKKCzXS51LGeYJ52QZJokBsyJp1WxzhIsYZ
thyUT7XRszcwuJmuAHs4gXNyyFoaOnv/bs3trtUYeetF95OjayjkAHYsy/GDBAk/7fW1MFH4e5a/
WCIEzvofk580Pnhod+BhY356F4iox7SvnaM+qPDuxg1jOeIMlLud7SyxjXrH+Eocx1PZCkXg8YLC
nE5hl3InIMXXXXGBOagCMFEe1I+69xkuD/H4iJUTCTCSBZs1uXzvoVvyAXG2RTb+a/U6z122aFz5
BrFD0Bh3irha4qBjNXl+M9b3RxWjmhRkwDHOS1LWKAuq6CD9uz6z1jOd1jRORdUy0bVe4C90a/Hs
DV7w6568jjS+TK/j7t9gGlpg31ZsnJBVjzb9upK1CO5O4pjBWRVywDYxqYqurJTEM9rA1g9DKlh+
DBwk0R7+Jsc8qZUuz9zfADKhqnONCMI8PLE/+bmMHw9Bvomi8g8rhUPfVH8y08AsJrNv66wZO1i3
wsNB7qzf2ggoek3LBAHrq2LdpelGV+mG4iuOoLQRPPp2CtrL8JeQo35J/mIMga/cHGzjPlafMiSg
4xXNadVvbNLLiZ/MZsb8mvT/CFY8JYpivRBfzkUCLFNM5LhZl/19F9+GgYPQjRNzddkzy711aTlG
E848B3k/6vn5G5XXB30O8yYALMSb+iJDno7OHoIssjuX6f79gkyoXTPeccMGfIpG+iWItalfBALA
Tv5TDOoFdNLA/SX2XNf7rhoOg7Bha+OiO5uOUnf/89lowagZapRVlhsUQESyiQDIeiDnLlrA4KRl
ytysqZtb3XWyn896bo98XfeJt470UvzLX7mWHoi0QAkEDMVQNgYquEG9dAk3nzIASGXvQnH2TIxH
vlQ35sW+HAUNhtVDVcv+shWl26mgFPmRf3HFsN4nYElnUGrJhw+D8/EIv7NrkbGsVGFmShNoZum1
M2QNUuclIZxO1dovPbYnIA1NQsPfimW2FzE0a87sR1lf0tUeOLVfJN1m4MKQut/soQdbXlhC6d/F
E3o7kfXy4xW6RSh7+WXTMC/ZhZ3RnKz6NAofBwiXwM3zUPPVYPzbnWIdL1Ak7+vQxx8p5T7g96an
5/K5Z1Mpyh4NHbcLENvu9zEN6h9eHxzgdSEOYrqj1OW81C2qwGCYFy6u2B1jQBOhUoz2FtHNoK1g
M0EbZJxwQC9ZYv5hb7NQEPTBbSiMb19e1G3p/Ilj2VErAmTJ9PGMyDf7df5Zc3Y25gUkbDZv1rwr
UfS/o8XPUzVKze4NIqJNc8PmNPSrMZpkFVUwW3dVerEYO59arrQ+WGuFNAYUa1wcrBetcrNXV7GC
lPlYQeaIFVetCsf/E9tOgXIDb8SfqfrbG3vy7+9HqrxyWr3KVW7To0oKjCQIFzMyDKsse7+QTNBF
3c1x9SvNIqOUH3NWLElSr9Z7E7PJcXh/92Yrv81NFbmFGLOsQLG3kjEQZvsli+Cp2Zru9gJ02yt8
X6EdEzBBqj3qTp6GgBRyNi4RQQMfQViHHJWhNRh1TbdTmL8XnkC3ncua1S6DD6w3l0QPitwGB82h
HR6RuQ1sMrvKSD2pup/XSc2Hd3Jp4E9YQJCQYaUlCyiS7DKRAUXRV99N6a34S1Sc3hhV3/bQrwRX
wfDvDQ7LvMLCgrKRlVXD+CmYCSQsYzHaMCeoK93B555bPANvvXPxEa82YMhOQS5a9Oen7YQlvOhv
LBD1yN2IyU/nSU4FauaGISHtwlB0G9odkBbAX2FRfTxBdMoSOWANR+jckXNCat9ENGErW97OKIx0
EygETSwrteVyhgFNARnfyLmpqZXnt3Bd+52sL8Wp4hvoCBWKEMAnPo0mHrESAH1ACu/YsA1a/xxg
jJQ8RUW05EouUxvPv9CemoqRTd+94cGaX6//vVYe+l0rLal2LpkgL5KRFjNNbg660emsEgR1cdi7
/6FAGCCf3CuRB8oB5PWgSpmkSgUMQ905q9JCRVoWuT6/d9ugzpSim0JZ6lZy43R3PEzdpDVNtgTi
jGi22VJF8GjMJwmzsTttDuAK9/854nVSv45T9tAGmUjTW5dvDbZSHnO3DaVfnBL9sVp6E1W/i4rR
V6sOlQNRTCVUhzh+UgKyGw1ilrYTyIFsH6BpqDm/2BcMQn1yUuvdZzg8s/ZxGwn2pjgjPOf3Vawt
+mr+Lai1HBANjolBR9yF3YHYw8+FXXI3gy1p+yc5jLIeKyfGOZJdZNan4cj96trWY24QtGyM7Rsb
wWWSNWXACAasMYr01PoUW5Spzv0hKIuOJ+EMBwfnoirPjGQch801dm0Gr4msOBVwzNLrhRV7SPLR
niV8w/OYHHfUMuR9LKDlnA7Cx6HO0TCkXgmEQHo8V+ci5C2sI9mSLkgnGthZjiqjjH4SD9VHijLu
NLxZyG2Wdr4j5SgT8+uSJF656vkHa4GJY6xYaokFWXgZFkkas4pAuaGvQeWfdn5BvC8Z+hENram1
0tMGvEn1teXkE0T5VzxIC5HrRFJ3qf9cmcfFWwtNUIGKLBV8MyNWUNa7/CVUy8c1va9nzpjn92tn
2jD5wNON0dwR0NiHZzab86gnp1LXDEB9yEatXcIYM3yIldX7cca1Ho1oGJnPlK/X2enTpY4edWQE
acXSzNieCgB3EpK7V47dQn3LdLwICF2lhvLoPRH1TqgMkOsvIBz1VNmhB/XhlYYXqA00hpMX7bCK
EbhKu3epDO+53aAKJSo7aBsFv07bUM2WedurglefDWKmkW4R4Y2tknnRWWwKqZTA6sk1PYq4xLea
NlqM3FW6j4XYigwSX/jiHPbqPHW36hAqsUj32Q74+kxhMbPALRRBkJ24lzpe3WkKX8Nw1BaY7ruP
YfPjb0vfow+gjgQO8iwJeU7b0QhQOM7fOUTP4I/frivznvIyH6hrH71MAlCPdh7AXe6tfEtAX5uZ
0QxY+DsmQPCFV5bbgo1eoWeEnXvTIf9DCiSXN0yphkgneNjS5r9o0eFcvXnMh02ps1CMHAo/hX+9
zyniNrM4iqytAmXJV1M9QMjLknlu6UUKYFicTJGm/xjew1bIcjDBhclpDFWSyYsU38nsnwOnHYQn
vCz0IPI1KLcklnSqvgY5JeEm7HW130KeFZ8fDPDfqm0bhG/MipYCYoPzXvtG4aI871rp/oO1hRLe
LyvGWqKh+IPAsBUKpnZOjx1Lk+KDNhOJyRrrLhkynBGS8Mz1xcTVc36RVAG429MBPlw3CxFijeg2
HvABYwSW1+Fj6tQctuZ68SYAH6ctVUqccrS4nds4e1I2fIqy3j4JRVuS5/GeJ8uKtB2NWxZmasvO
ko/VjtjOWLfrT0TnWH319rCUH2mCdsjPqpSD/ozKzQjMdJpzIk9ZvujfEPJPXJIkQjYG20GgjiIv
bdvzcvy3sMaiZ5kp3486YcgRgQB2fShTBYPRiOdhVU927YSZ4Km6UQLoY/rABtH4oBkSadsFgfyy
wNjPr2ioCTV4zlAR4jnJKhtESOKIWLTL9fWAASkDE4hI2TnVgVJgYIzAmzjgiHzN79UZ5jjwh3Yk
sMjsln01gNLV7HyoQZm49toV7BrZxxw7X027o/X6toKo4BjKzi9naA5G2crgBeO6B0U9LnfauGqO
a7dAkVsKvdErlWwxiiD+hkevXOMDB6sdrjbq3gjCyeYbQoEipSNmtvi6r1AFtpCZQpYsjp957jMR
g0ZCDJJrn29JGjxRi9MO3axhYMejZHF5TzCKEfBhO5f6/UsYEM44/VcZAQawXTifAGEBE7yUsVi2
8cwrtGcolXASlmDVl6Gt/q3OTYgBA9HLfWIImjjQRbCQa0vP1Z5pOXiSFByUlLm5hwuST7E9gEs9
4NxC877i/iT39TTTUJ8XGzYlMnzt3uvGR4eFTcA6oD/V0BTkP5nI0ozRNY/8PUUeVoI4rX7iNFFB
icJxICs9VvswLoOndZLTWOSKJiZlV4seGfEImE3/ViS+7dIkMbsB+wQpPl/qDyU36J7Gi9lcIEMg
nh0BNgy3t7AvcMvOaXk4pvmw9epPTFl/eAWyrDiM84jLWyK6Qz6Skg6AjfxPHJWxV6/E2orlDaTS
NRgPk0vJRCXw6mHZzoSji9QeC7hDhpc6H81KcmMeqU0094P0yjV4MUFAzqnEQMwNwvQ9xHsCAsoT
nz2J8fo4Yf8TdZH8nOILQaeN465SNEALJGz9NYBKltcxpd1WqC9XtkA+U3FGdlnCtHlxB2OUhbAs
Af88QFQzNec3vfqjxTSeoNctdklEG+Z4masw1TmfxUfoJG652J5f7RnKsK3vaSrDHxXZpRdWwjLr
L8FJrBXNlDb2JKCqWoJk2FFV3kmrA++8fNl9b0SbBbs6u5+93qpDpJWYWLXFVqEaWeagH14zABM6
eMG1UuF0OPGFd8y86+xeG8mdUOMEhk94UFpmlBnPW4NpFktUv+zcxjpK4ysgPTupUGRM1Yvt5LWo
XpOtaQjp+uj30fH7ZzQ8709FYR9vPWCEgt7Qg0nEqnZ8i7fGqpuC38yz7mSnpeaI6sZXlpYOqiO2
8SQnPvdWVIubCw6uyv3MG2odqmkZb51dv5KkZDvK0f/ZdyXfeXQxWFv48a3CXxxKR6r7bJOLVkfn
5kaNJ25ikZqDSXrSTZ82WKhzibS+4AMw4XdkY/x1L9YAakvt8xIKYjtbEN/8pZTR++9PRrtp7uPt
VRMXqAl4Jwwev+1fLjANkUNQxWK4PwsxNIU2m9vq6cRIqVi8gB2GhkZfYwy5RX67cwgwEcrZQwQH
ck26l24pvAZFzFJN0brdtDqzlyxKhdJBrdX41VSpBah+xWl8KpulWdjq6pn5lKP0EtktJjVmcfPA
Cmb+r3Hl6g/c9k9DaFcBFUfQZyqIH6vXkEbhK4wmtJbqIyGim+15LwkTFodXeI3WMoX5V3EKA54Q
Yafyqu+qNvy4fI7B6kF3xismI/EbdVervTUywvzjy7iSAB9ReXo16J0D2NJYxrdgkAe1qkLt13Uu
n9b8ckz+0Bke20vWEjVnVaXR+WcxQx2nh3IlO4KCCKOzaMXYHFuvVRfo613nnuFJsazRsjNp+4vE
f9ZlPgaiTV6XW9Yf5NtE6Au7FnInIfhxf9kO+IX2i8lN/6g0avPpaFPH2iY3nUGOJtY3wJr/hWhq
rPxh2Noce0BdqrW19B5DHrI6BXLvJE0JqNuAaRdCmyLY3I7t3yZg8Eqwi4oYi5kbmJu3/kawIDMl
M+GJ1gZ7Hrtrw5z/NJiS4snrOLs+lkFrQsKYaBecXe3M0IxPyqzF/ZsPP1qGnL1IR0P1uyAsNrvQ
vgpgYECFfaeo3ZchTPP4sahurHuajBq8MnfCnXQWsE2ugWHWyeBujvqxZEAa9IOATSHp9lUJh5Sq
5hkfFmHZQjy9WRXI/GShA4gaR36Qk4fo0PDARfZE1BgkpKYcK611Db4uoyJygxuTq+okOSpRV10t
C1ntcAA4YiS+kt1MN/CRPHoJWvoM5bB9T9XLnzKV2fDgR4HPvcK3DD4L7ZAjngRkxWOSA964nSdl
g3elOuyUXH8ceWcYtIAKU+Cepcp6AeLqqHEOimpAU9dGnBSNCPAMRA0nHWKCclSQgTmstWLEjUL4
gxOrpqNU3nHRVndpsyMZO6FUKIXMUh7BEKfEMtFcGl1uLbRgYtjXXhl6GVePRIv0QADbswfB7tpC
fApt1w7H0XqKRZcMyOyjveZcxjNdDzvWHkv4zEqmhHMC/O9rm/xcGuTfDPmEz6h7wn75m31jj/5M
mwxkc5hA8Kse7OBapuGASWTTM8YbhdmYHOrNhdF+NOu5cEELOylWHhnppTS1PZZLe3xtqUwngbAJ
uMufr/moK0zX1taoCSS4Gds+4Xg/7wey/dglZYNN3RD6XjHPqaVgVRuBhGdhmRzquECqJ1bdl98z
dE75psgTRYWCwtYvc5PGjawMZ4WYOzTgII4SDk5biVwOqd3qMAGzDSJ4y31hxLBaxTT4OmoPCA/s
GGpjTAs8sd9ZB8EAikk+/WkyIAqFG9K4i8sXX9OCI4G1oah5e4/0Y4VPsZtZhzK4GXrCPTqSaHsv
v+N7SgN+THoTAqDWJ66dTzKWTnBrEEEoEQYQhjQ+mam6HFJ3rVmllkY4VpNLThXvmxx3qB/lUl5f
NR5lRWHBLCt04Rn5Y5qVAyAS589Bt6BR71MbrZDXyYlluceIdvM5j9nezfVe+E8/6OVMLtJv44K3
zA0dLk8yrLPPsNzZz20ybU5/z5LQzJsS6o4NDL0aKjhrkixTxPdBFkRxIo6dEUPP5TW4gJ2045iL
hNojWGVuEPva0WjhiVJtnvAnIwaIlY221JKoZ9NoY+0QBFw0RC46XKTJLqxcr/KtG1txY5W8bBxb
8XVZyNRgPG6L4mKFaUySPO8XhPxPe2z9WPdupv29EQrfrL4gTStcb02Ji7mBwB/Zw/yJhXaV5a5c
/FQfK98sOK8gojmR2eN+uIWbdaTAuKiqV1VdQ/Rm+li9cCf1JAOlyuhDNLFmvMxbtajVFc7d+5vZ
ZP/O65H1/ZldWXoHv9nGBK5vnTEgIoUMKC1g0Mzu2GNxV2XDoG6N/LVr8000wREVuvGPqdRhqDoT
sfp21aIT6uYV+rgRTv9yrR/Or8bpTcJf5k6JdTn4PFHkMPVylqfRd8fWPaREsQpzBrF+bVcFHQK6
lL0mZV7etqGvUTBaCu31aHkoixokk9D3a1phRFO/aon//Nqru0cpq6GvJBUxnveL4C6V+S+MXv4Q
sO3jfvpJaSzgxgidOQHJ0f1RiQbkUZVAMC04lbUpVUg1fOzI1HQGLAozfY2qBO/B2Ap2FUNQybTU
AIhX1czOqHjTQj7BYo+pk9EbntYZNLifxr0+8inblHdqd6QUzMZmcqWropCFXtA3eM0CJecqhQqb
05yBcXIN+44GHenfKUx8Vpp1TMkKpmt/sj/cZj4Dq3wzHQwOHSwsKI63Km4E6yO8cDqyDPaWsi4V
49op2MjTHkNY1dE=
=BPsZ
-----END PGP MESSAGE-----
End of the Story
Today, ISPs offer automatic backups, often using RAID-X volumes to store content. This setup is basically a clone of your master disk; if one disk fails, a second disk goes active. This is another easy possibility for someone to get data.
Not with my mail system.
Even if you were able to decrypt my passphrase, you would still need to do the same for all the other users. Every email is encrypted individually using the recipient’s unique keys.
I cannot access the emails anymore
Key Generation and Trust Models
Contrary to general standards, I decided to generate the keys myself and combine them with a login and a private key phrase (passphrase). Someone could accuse me of having stored the passwords and private keys during the creation process, which is theoretically possible.
This is not meant to be an accusation against providers like Proton, for example. After all, it is now possible to create and upload your own keys there. However, the average user thinks everything is secure, but it’s not: Proton created your key and knows the password. ![]() Again this is no offense against Proton. They concept is make money while we have fun, testing technologies.
Again this is no offense against Proton. They concept is make money while we have fun, testing technologies.
During the automated key creation, or change password process it’s possible for the data to be intercepted and stored elsewhere.
So, what remains? The user must take matters into their own hands and create their own key and enable end-to-end encryption.